CHINA’S ILLEGAL CYBER INTRUSIONS ALERTS WESTERN INTELLIGENCE
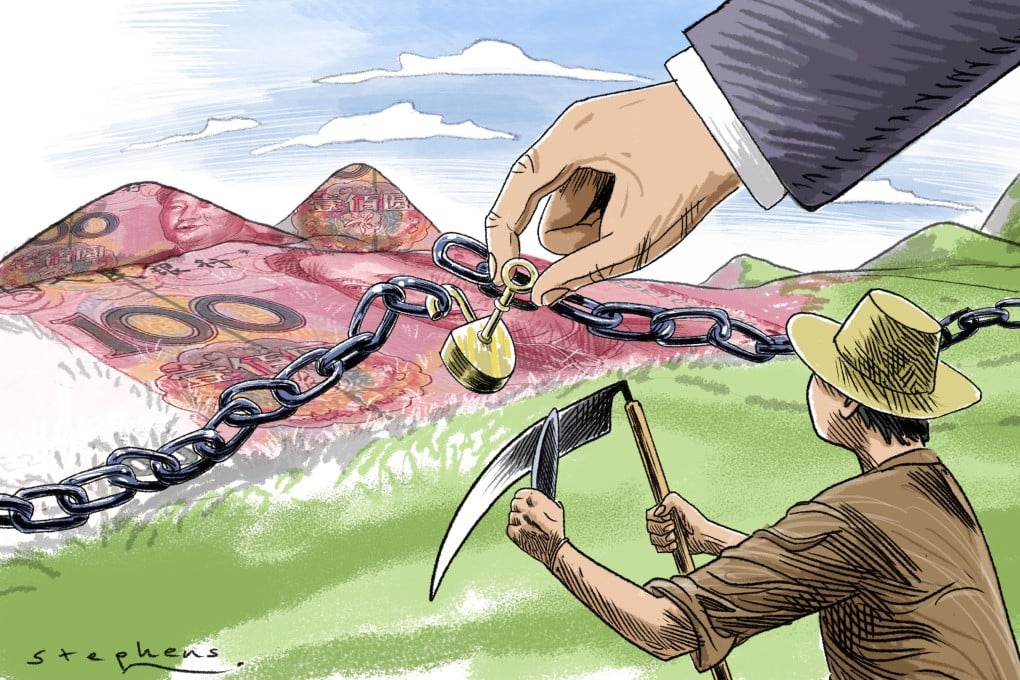
American intelligence and cyber security agencies have recently exposed how China leverages cyber operations to “assert its political and economic objectives” and worse, is reportedly attempting to influence real-world activity in targeted countries.
The Cybersecurity and Infrastructure Security Agency (CISA), National Security Agency (NSA), and Federal Bureau of Investigation (FBI) have conducted probes that confirm that “Chinese state-sponsored cyber actors aggressively target US and allied political, economic, military, educational, and critical infrastructure (CI) personnel and organizations to steal sensitive data, emerging and key technology, intellectual property, and personally identifiable information (PII)”.
Fireeye, a well-known American cyber security agency, in a separate investigation, found that the Chinese cyber actors who, in 2019 operated a network of hundreds of “inauthentic accounts on Twitter, Facebook and YouTube, that was at that time primarily focused on discrediting pro-democracy protests in Hong Kong, have since then broadened and expanded their activity “in size and scope and received widespread public attention following Twitter’s takedown of related accounts in August 2019”.
Other researchers and cyber specialists are at present conducting fresh probes into Chinese hacking and cyber-crimes. These include Google’s Threat Analysis group, Graphika, Australian Strategic Policy Institute, Stanford Internet Observatory and Hoover Institution, and Centre for Information Resilience.
US intelligence assesses have throughout 2021 assessed China’s “prolific and effective cyber-espionage threat (that) possesses substantial cyberattack capabilities, and presents a growing influence threat”. They say that the Chinese cyber-spying operations include “compromising telecommunications firms, providers of managed services and broadly used software, and other targets potentially rich in follow-on opportunities for intelligence collection, attack, or influence operations”.
The objective of the Chinese cyber-crime operations appears to be not only to spread propaganda but also steal information and technology from the “US government, CI, and private industry organizations at risk of loss of sensitive data and technology, trade secrets, intellectual property, and PII”.
The cyber actors target political, economic, military, educational, and CI personnel and organizations. The sectors targeted include “managed service providers, semiconductor companies, the Defense Industrial Base (DIB), universities, and medical institutions”.
The CISA report says the Americans are fully aware of the Chinese cyber intrusion and have taken action against it: “During the past several years, the Department of Justice has charged, indicted, or sentenced PRC-affiliated cyber actors with computer intrusion campaigns targeting multiple CI and private sector organizations. Some of these actors attempted to obtain and transfer sensitive US software and technology to China.”
Fireeye, meanwhile, says in its probe report that China is at present promoting “a wide variety of narrative themes related to current events, including multiple narratives related to the COVID-19 pandemic, narratives critical of Chinese dissident Guo Wengui and his associates, and narratives related to domestic US political issues”.
On the expanding scope of China’s cyber-crimes, the report says: “The scope of activity, in terms of languages and platforms used, is far broader than previously understood. Most reporting has highlighted English and Chinese-language activity occurring on the social media giants Facebook, Twitter, and YouTube. However, we have now observed this pro-PRC activity taking place on 30 social media platforms and over 40 additional websites and niche forums, and in additional languages including Russian, German, Spanish, Korean, and Japanese. While some platforms have hosted hundreds or thousands of accounts in the network, other platforms have hosted a smaller number.” In effect, the propagation in many languages and new platforms means China is attempting to reach out to new audiences in new lands.
The report has video grabs of posts from various fake accounts on diverse websites. “These accounts have posted similar, and in many cases identical messaging and engaged in the coordinated sharing, commenting on, and liking of text, image, and video content.” The report gives an example: “Thousands of identical text posts, images, and videos promoted by accounts on Vimeo, Vkontakte, TikTok, and a number of other platforms claiming that Chinese dissident Guo Wengui, former White House Chief Strategist Steve Bannon, and Chinese virologist Dr. Li-Meng Yan are ‘liars’ in response to Dr. Yan’s Claim that the coronavirus was created in a Chinese lab”.
There is another example Fireeye comes across: “In April 2021, thousands of posts in languages including English, Japanese, and Korean, images, and videos were posted across multiple platforms by accounts we assess to be part of this broader activity set that called on Asian Americans to protest racial injustices in the US. The accounts specifically called on Asian Americans to protest on April 24 in New York City and ‘fight back’ against the purported ‘rumors’ caused by Dr. Li-Meng Yan, Guo Wengui, and Steve Bannon, and in ‘…some instances provided an address that they claimed Guo lived at’.”
The Fireeye report issues a warning: the attempt to physically mobilize protesters in the U.S. provides early warning that the actors responsible may be starting to explore more direct means of influence and may be indicative of an emerging intent to motivate real-world activity outside of China’s territories.”
The CISA says all top countries today face cyber threats from the Chinese and that they should develop a culture of cybersecurity investment and strategy. “Ensure your company follows best practices for cybersecurity including employing multi-factor authentication (MFA) and keeping software up to date.
Ensure your organization has incident response plans. Ensure personnel are familiar with the key steps they need to take during an incident, have the accesses they need, and are positioned to act in a calm and unified manner. Ensure personnel know how and when to report an incident. Flag any known Chinese state-sponsored indicators of compromise (IOCs) and tactics, techniques, and procedures (TTPs) for immediate response.”